- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 03:03 PM in
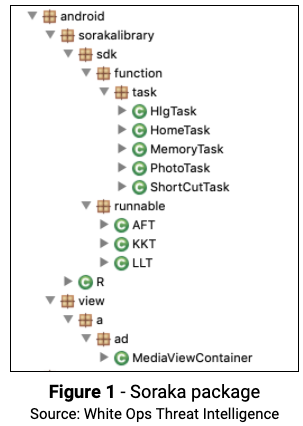
Galaxy SThe White Ops Threat Intelligence team recently identified 100+ malicious apps, with more than 4.6 million downloads, performing ad fraud. All of the apps use a common code package White Ops has dubbed “Soraka” (com.android.sorakalibrary.*😞
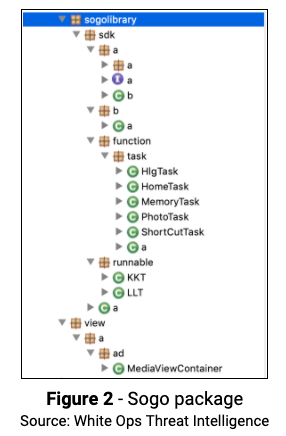
In addition to the Soraka code package, we also discovered, in some of the apps, a variant with similar functionality which we dubbed “Sogo” (com.android.sogolibrary.*😞
Best Fortune Explorer App
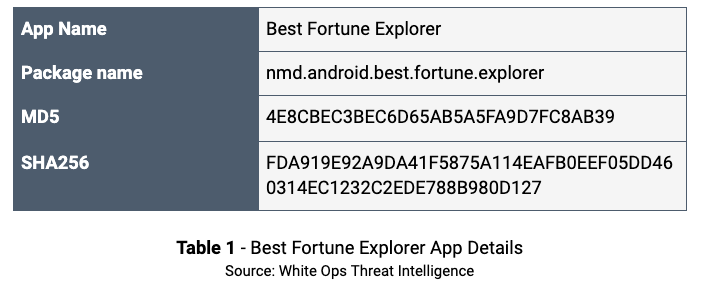
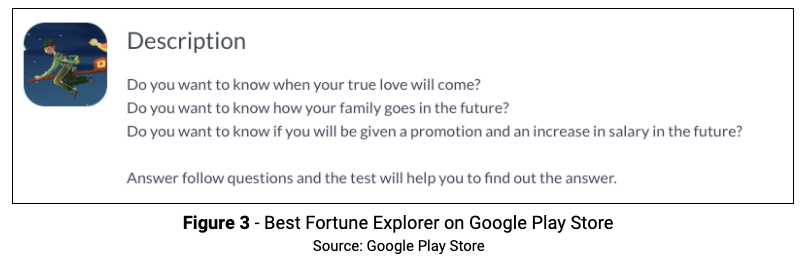
One example of the Soraka package was the “Best Fortune Explorer” app by the publisher JavierGentry80. This app was released on September 9, 2019 and is the only app published by JavierGentry80. Best Fortune Explorer is, as of this writing, available on the Google Play Store and has no Anti-Virus (AV) detections on VirusTotal. This app has more than 170,000 downloads.
Fraud Activity Filters
The apps are using a framework called AppsFlyer for mobile attribution and marketing analytics. The app displays fraudulent ads only if AppsFlyers determines the installation is NOT organic, meaning the install was attributed to a promotional effort by the fraudsters. There are several filters the code checks before a fraudulent ad is shown to the user:
- Screen On
- TopActivity
- Interval since installation
- Trigger on/off switches
- Ad Network daily count limit
- Trigger time interval (to space out the ad rendering for each trigger)
The filtering is likely a mechanism to avoid detection from automated analysis and other services that would install the app ad-hoc and then, most likely, be considered as organic by AppsFlyer.
This mechanism also allows fine-grain control of who (or what) receives the ad fraud, using the controls of ad serving platforms. The apps render out-of-context ads when the filter conditions are appropriate.
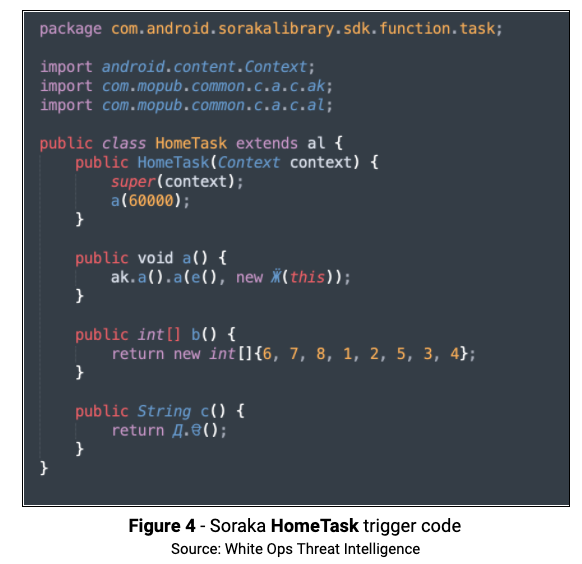
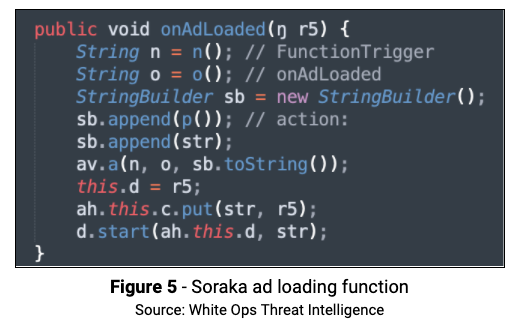
The Soraka package can be found in com.android.sorakalibrary, and utilizes several triggers to make the determination of what to run. As an example, int[ ] b( ) returns an integer array of filters this trigger (pressing the Home button) needs to check before running. The method public String c( ) in HomeTask returns the name of the trigger. All of the trigger classes implement this method, each returning its name. To further obfuscate the code and make analysis more difficult, HomeTask creates a class named with the Cyrillic character Ӝ, which is part of the Udmurt language. The class Ӝ goes to a Mopub method ah where the onAdloaded function is called to start the ad rendering process.
Ad Fraud
White Ops Threat Intelligence identified the following ways the app rendered ad fraud:
- Upon unlocking the device, the app code removes the background notification service that halts all fraud activity while the phone screen is off.
- The first Out-of-Context (OOC) ad (shown below) is rendered a couple seconds after the device is unlocked.
- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 03:39 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 03:43 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 03:49 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 04:00 PM in
Galaxy STested. So that crap apps would not be propagated.
Hey, I like the term CRAP-Apps 🤪
Really
This should not be happening.😖😖😖😖😖
- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 05:22 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 06:14 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 06:25 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 06:48 PM in
Galaxy S- Mark as New
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2020 06:50 PM in
Galaxy S